Cloud Security Technology as the Foundation of Secure Digital Transformation
Cloud Security Technology plays a vital role in modern digital transformation as organizations increasingly rely on cloud environments to store data, run applications, and manage critical business operations.
The shift from traditional on premise infrastructure to cloud based systems has changed how security must be designed, implemented, and maintained. While cloud computing offers flexibility and efficiency, it also introduces new risks that require a structured and comprehensive security approach.
This article explores cloud security from a strategic and technical perspective, providing clear insights into how organizations can protect their cloud assets, maintain regulatory compliance, and build long term trust in a digital economy.
The Evolution of Security in Cloud Computing

Cloud computing has evolved rapidly over the past decade. Businesses now operate across public, private, and hybrid cloud environments that are highly dynamic and interconnected. Traditional security models, which relied heavily on fixed network boundaries, are no longer sufficient in this landscape.
Cloud Security Technology emerged as a response to these changes. It focuses on protecting distributed systems, remote access points, and continuously changing workloads. Security is no longer a static setup but an ongoing process that adapts to real time threats and business needs.
As cloud adoption grows, organizations must rethink how they manage identity, data protection, and system monitoring across multiple platforms.
Why Cloud Security Is a Business Critical Priority
Cloud environments often host sensitive customer data, financial records, and proprietary information. A single security incident can result in operational disruption, legal consequences, and loss of customer confidence. For this reason, cloud security is no longer limited to technical teams but has become a strategic concern for leadership and governance.
Cloud Security Technology helps organizations reduce exposure to cyber threats while supporting innovation and scalability. A strong security framework allows businesses to expand their digital services without compromising safety or compliance.
In competitive markets, organizations with mature cloud security practices are more likely to earn trust from partners and customers.
Core Principles of Cloud Security Technology
Effective cloud security is built on a set of core principles that guide how systems and data are protected.
The first principle is visibility. Organizations must have clear insight into their cloud assets, user activities, and data flows. Without visibility, security risks remain hidden until damage occurs.
The second principle is control. Security policies must be enforced consistently across all cloud services and user roles. This includes access management, data usage policies, and configuration standards.
The third principle is resilience. Cloud security strategies must assume that incidents can happen and focus on minimizing impact through rapid detection and response.
These principles form the foundation of Cloud Security Technology and guide the selection of tools and processes.
Identity and Access Management in Cloud Environments
Identity and access management is one of the most critical components of cloud security. Cloud platforms are accessible from anywhere, which increases the risk of unauthorized access if credentials are compromised.
Strong identity controls ensure that users only access the resources necessary for their roles. Authentication methods such as multi factor verification and role based access policies help reduce the risk of breaches.
Cloud Security Technology integrates identity management with monitoring systems to detect unusual login behavior and enforce adaptive security measures.
Data Protection and Privacy in the Cloud
Data protection is a central concern in cloud environments. Organizations must safeguard data throughout its lifecycle, from creation and storage to transmission and deletion.
Encryption is a key element of cloud data security. It ensures that even if data is accessed without authorization, it remains unreadable. Secure key management practices are equally important to prevent misuse or loss of encryption keys.
Cloud Security Technology also supports data classification and access auditing, helping organizations comply with privacy regulations and internal policies.
The Shared Responsibility Model
One of the most important concepts in cloud security is the shared responsibility model. Cloud service providers are responsible for securing the underlying infrastructure, including physical data centers and core networking components. Customers are responsible for securing their data, applications, and access controls.
Misunderstanding this model often leads to security gaps. Organizations may assume that cloud providers handle all aspects of security, which is not the case.
Cloud Security Technology helps bridge this gap by providing tools and frameworks that support customer responsibilities within cloud platforms.
Cloud Security Tools and Supporting Technologies
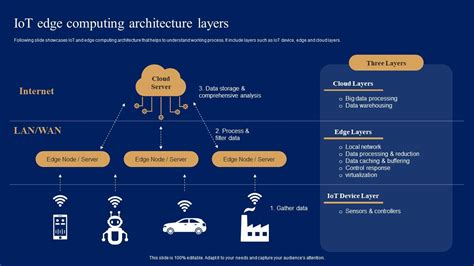
The cloud security ecosystem includes a wide range of technologies designed to address specific risks.
Cloud access security solutions help organizations monitor and control how cloud services are used. They provide visibility into user activity and enforce security policies across applications.
Workload protection tools focus on securing virtual machines, containers, and serverless functions. These tools detect vulnerabilities and protect workloads during runtime.
Security monitoring platforms collect and analyze data from cloud environments to identify potential threats. When integrated properly, these tools enhance the effectiveness of Cloud Security Technology across complex infrastructures.
Compliance and Risk Management in Cloud Security
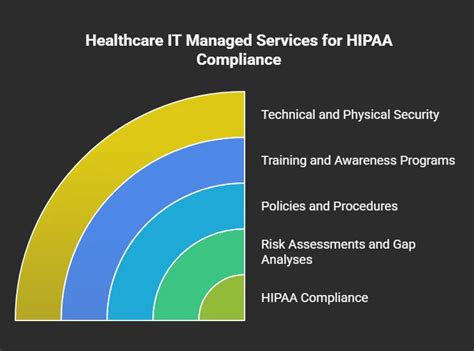
Many organizations operate under strict regulatory frameworks that govern how data must be handled and protected. Compliance requirements vary by industry and region, but they all demand strong security controls and transparent reporting.
Cloud Security Technology supports compliance by enabling continuous monitoring, automated audits, and detailed activity logs. These capabilities help organizations demonstrate accountability and respond quickly to regulatory inquiries.
Risk management is an ongoing process that involves identifying potential threats, assessing their impact, and implementing mitigation strategies aligned with business objectives.
Best Practices for Strengthening Cloud Security
Organizations can improve their cloud security posture by adopting well established best practices.
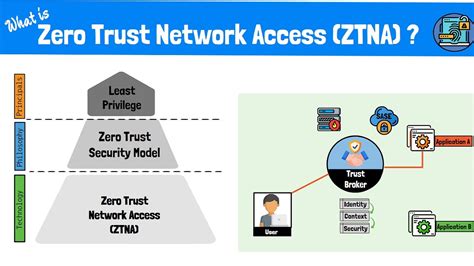
A zero trust approach ensures that every access request is verified, regardless of location or network. This model reduces reliance on perimeter based defenses.
Automation plays a critical role in maintaining consistent security controls. Automated policy enforcement and configuration checks reduce the risk of human error.
Regular security assessments help identify weaknesses before they can be exploited. Continuous improvement is essential to maintaining effective Cloud Security Technology in a changing threat landscape.
The Impact of Artificial Intelligence on Cloud Security
Artificial intelligence is transforming how cloud security threats are detected and managed. Machine learning algorithms analyze large volumes of data to identify patterns that indicate malicious behavior.
AI powered security systems can respond faster than manual processes, reducing the time between detection and remediation. Automation also helps security teams manage complex environments with limited resources.
As threats become more sophisticated, the integration of AI into Cloud Security Technology will continue to grow.
Common Challenges in Cloud Security Implementation
Despite advanced tools and frameworks, organizations often face challenges when implementing cloud security strategies.
Configuration errors remain a leading cause of cloud security incidents. Misconfigured storage or access permissions can expose sensitive data.
Lack of expertise is another common issue. Cloud security requires specialized knowledge that may not be readily available within all organizations.
Addressing these challenges requires a combination of training, process improvement, and investment in appropriate technologies.
The Future of Cloud Security Technology
The future of cloud security is shaped by increasing cloud adoption, evolving regulations, and more advanced cyber threats. Organizations are moving toward integrated security platforms that provide unified visibility across multiple cloud environments.
DevSecOps practices are becoming more common, embedding security into the development process from the start. Privacy focused technologies are also gaining importance as data protection expectations rise.
Cloud Security Technology will continue to evolve as a critical enabler of secure and sustainable digital growth.
Conclusion
Cloud Security Technology is essential for organizations that rely on cloud computing to drive innovation and efficiency. By understanding core security principles, adopting best practices, and leveraging modern tools, businesses can protect their digital assets while supporting growth.
A well designed cloud security strategy does more than prevent attacks. It builds trust, supports compliance, and ensures long term resilience in an increasingly digital world.