10 Cloud Security Technology Risks Businesses Must Address Before It’s Too Late
Cloud security technology now underpins core revenue systems, customer data platforms, internal collaboration, then operational analytics. Adoption accelerates delivery speed, yet the security model becomes more dynamic than traditional on-prem environments because cloud assets are created, modified, then decommissioned continuously through automation. That velocity produces a new kind of risk. A single misconfigured storage policy can expose confidential records worldwide within minutes.
A compromised identity token can grant access across multiple services, then pivot into production workloads. A rushed SaaS integration can introduce excessive permissions that remain unnoticed for months. These problems rarely begin as “advanced hacks.” They often start as ordinary engineering decisions made under deadlines, then become exploitable because monitoring is incomplete, ownership is unclear, or policy enforcement is inconsistent.
Businesses that win in cloud security treat it as an operating system measurable, automated, continuously validated, then aligned with the shared responsibility model. The ten risks below outline where cloud security technology programs most often fail, then what must be addressed before incidents become costly.

1. Misconfiguration Exposure Across Storage, Networks, and Access
Misconfiguration is a leading driver of cloud breaches because cloud defaults and rapid provisioning make it easy to expose assets unintentionally. Public object storage, overly open security groups, permissive firewall rules, then unmanaged internet-facing load balancers can reveal sensitive systems without any malware involved. The most damaging element is speed. Infrastructure-as-code can replicate a bad setting across environments quickly, then “temporary” exceptions become permanent because nobody revisits them.
Strong cloud security technology reduces this risk with policy-as-code guardrails, baseline templates, then continuous configuration drift detection. Controls should block risky deployments at the pipeline level, not only alert after exposure. Visibility matters too. Teams need an up-to-date inventory of storage buckets, databases, endpoints, then IAM bindings, because unknown assets cannot be secured. A mature approach includes automated checks for public exposure, default encryption, logging enabled, then least-privilege network segmentation.
2. Weak Identity and Access Management
Cloud security is identity-first. Attackers increasingly target credentials, session cookies, API keys, then OAuth tokens because those artifacts provide clean access without triggering traditional perimeter alarms. A single overprivileged account can open the door to broad administrative control, then enable data exfiltration or destructive actions such as deleting backups. Effective cloud security technology relies on least privilege, role-based access control, then strong authentication such as multi-factor authentication and conditional access.
Yet least privilege alone is not enough if access is not time-bounded. Short-lived credentials, just-in-time privileges, then approval workflows reduce the window of misuse. Another common weakness involves service accounts and machine identities. These accounts often have high privileges and long-lived secrets, making them attractive targets. Businesses should manage machine identities with secret vaulting, rotation, then strict scoping. Logging and alerting on privilege escalations and token anomalies completes the control loop.
3. Overreliance on the Shared Responsibility Model
Cloud providers secure the underlying infrastructure, yet customers remain responsible for configurations, access management, application security, then data governance. Confusion about this division is a persistent risk. Teams may assume encryption is “automatic,” logging is “enabled,” or security hardening is “handled by the platform,” then discover gaps during an incident. A resilient cloud security technology program translates the shared responsibility model into explicit ownership and controls.
Each service should have a clear control map who configures network rules, who manages IAM roles, who enforces patching, then who verifies backups. Documentation alone is insufficient. Controls must be operationalized via checklists embedded into release processes, architecture reviews, then automated compliance scans. Training is equally critical because new engineers may not understand how quickly cloud settings can expose data. A practical approach includes periodic tabletop exercises that test responsibilities, ensuring teams know what the provider covers and what the business must secure.
4. Inadequate Visibility and Logging Across Cloud Services
Cloud incidents are often discovered late because telemetry is fragmented across services. Without centralized logging, teams cannot correlate identity events, API calls, workload behavior, then data access. That fragmentation creates blind spots. An attacker can create a new access key, enumerate storage buckets, then exfiltrate data while security teams see only partial signals. Strong cloud security technology requires end-to-end observability unified logging, consistent retention policies, then normalizing data into a central platform such as a SIEM.
The goal is actionable clarity, not noise. Alerting should prioritize high-signal events such as new admin role grants, unusual data download volumes, access from improbable geolocations, then disabling of security services. Visibility also includes asset discovery. A live inventory of cloud resources and identities reduces the time spent guessing what exists. Finally, logging must be protected. Attackers often try to tamper with logs, so immutable storage and restricted log access are essential.
5. API and Integration Risk With Third Parties
Cloud ecosystems depend on APIs and integrations payment gateways, customer support tools, analytics platforms, then marketing automation. Each integration introduces permissions and data flows that can expand the attack surface. A common problem is excessive OAuth scopes. An app that only needs to read calendar events may request full mailbox access, then retain that access long-term. Another issue is secret sprawl. API keys stored in code repositories or shared in chat tools become easy to leak.
Effective cloud security technology requires a complete integration inventory, permission reviews, then a governance process for approving and renewing third-party access. Secrets should live in a managed vault with rotation policies, not in environment variables scattered across systems. Vendor risk also matters. A breach at a third party can become your breach through data sharing. Contracts, security questionnaires, then continuous monitoring help, yet the strongest protection remains least-privilege integrations and strong segmentation so one compromised connector cannot access everything.
6. Data Leakage Through Poor Classification and Over-Sharing
Cloud makes collaboration simple, but that convenience can cause unintentional exposure. Sensitive data may be placed in the wrong storage tier, shared with broad groups, then replicated into analytics systems that lack strict access controls. Many leaks are not attacks. They are operational mistakes a spreadsheet shared publicly, a development environment connected to production data, then a misrouted backup exported to a lower-security region.
Strong cloud security technology reduces leakage through data classification, labeling, then access policies tied to sensitivity. Controls such as DLP, CASB, then automated sharing restrictions can prevent risky sharing patterns. Encryption helps, yet encryption alone is insufficient if access policies allow everyone to decrypt. Businesses also need clear retention rules. Keeping data longer than necessary increases exposure. Good governance defines where sensitive data may reside, who may access it, then how it must be monitored and audited.
7. Key Management Failures and Weak Encryption Practices
Encryption is foundational, yet key management is where many programs break. Keys may be shared too broadly, rotated inconsistently, then stored across multiple systems without visibility. If attackers gain access to key management roles, encryption becomes meaningless because they can decrypt protected data. Strong cloud security technology requires centralized key management, strict separation of duties, then least-privilege access to key operations. Key rotation should be enforced, not optional. Auditing should track who accessed keys, when, then for what reason.
Another common risk involves customer-managed keys versus provider-managed keys. Customer-managed keys provide more control, yet they also require stronger operational discipline. Businesses should align key strategy with threat models and compliance requirements. Backup encryption keys also matter. Losing keys can be as damaging as leaking them because it can render critical data unrecoverable. A mature approach includes secure backups, tested recovery procedures, then clear ownership.
8. Workload and Container Vulnerabilities in Cloud-Native Stacks
Cloud-native architectures rely on containers, orchestration platforms, then serverless functions. These technologies improve agility, yet they introduce new vulnerability classes. Container images may include outdated libraries, vulnerable base images, then embedded secrets. Kubernetes clusters can be misconfigured with overly permissive network policies or insecure dashboards. Serverless functions can be exposed through insecure endpoints and insufficient input validation. Cloud security technology must adapt to continuous delivery.
That means scanning images during build, enforcing signed artifacts, then monitoring runtime behavior for suspicious activity. Patch management should focus on rapid remediation cycles, not quarterly updates. Another overlooked risk is supply chain compromise. Dependencies pulled from public repositories can be poisoned. Businesses should implement dependency pinning, trusted registries, then software bill of materials practices. Runtime protection, least privilege for workloads, and strong segmentation help prevent one compromised service from becoming a full environment compromise.
9. Insufficient Incident Response Readiness in the Cloud
When a cloud incident occurs, speed matters. Yet many organizations discover they lack playbooks, access paths, then tooling to contain threats quickly. An account compromise can spread across services in minutes. Without rehearsed procedures, teams lose time deciding who does what, which logs to pull, then how to rotate credentials safely without causing outages. Mature cloud security technology includes cloud-specific incident response planning predefined containment actions, automated key rotation, isolation of compromised workloads, then rapid revocation of tokens.
Forensics must be considered too. Logs, snapshots, and audit trails need retention long enough to investigate. Tabletop exercises help teams practice decisions under pressure and validate that runbooks work. Incident response also requires coordination with legal and compliance teams, especially when breach notification rules apply. The goal is not only to “fix” the issue, but to preserve evidence, limit blast radius, then communicate clearly to stakeholders.
10. Compliance Drift and Audit Gaps Across Multi-Cloud Environments
Compliance is not static in cloud environments. Controls drift as teams deploy new services, change configurations, then adopt new SaaS tools. Multi-cloud strategies multiply complexity because each provider has different identity models, logging formats, then security tooling. A point-in-time audit may pass, yet risk can return the next week. Strong cloud security technology approaches compliance as continuous monitoring. CSPM tools can detect drift in configurations and map controls to frameworks.
Evidence collection should be automated where possible, reducing manual screenshot-based audits that miss changes. Policies should be standardized across clouds consistent encryption requirements, centralized identity governance, then common logging and retention rules. Compliance also intersects with data residency and cross-border transfer requirements. Businesses must know where data is stored and processed, then ensure controls align with contractual obligations. Continuous compliance reduces surprise findings and helps security teams focus on real risk rather than paperwork churn.
Conclusion
A strong cloud security technology posture is built through continuous control, not reactive patching after incidents. Misconfiguration risk demands policy guardrails, drift detection, then hardened defaults. Identity risk requires least privilege, MFA, just-in-time access, then disciplined management of machine accounts. Shared responsibility confusion must be replaced with explicit ownership and operational controls. Visibility and logging must be centralized and protected so teams can detect anomalies early and investigate confidently. API integrations and third parties require permission hygiene, secret rotation, then ongoing vendor governance. Data leakage is minimized through classification, DLP-style controls, then strict access boundaries that match sensitivity.
Encryption must be paired with mature key management and separation of duties. Cloud-native workloads need secure pipelines, supply-chain defenses, then runtime monitoring that fits continuous delivery. Incident response must be rehearsed and cloud-specific, with automation that reduces response time and protects evidence. Compliance drift requires continuous monitoring and standardized policies across environments. Addressing these ten risks early keeps cloud adoption fast without turning speed into exposure, allowing businesses to scale with confidence while protecting customers, revenue, then long-term trust.
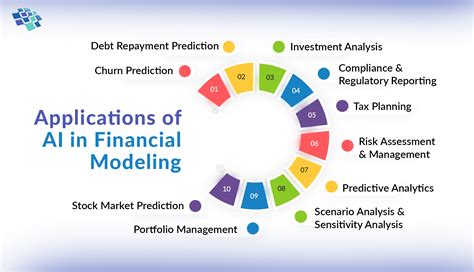
Read more: 10 Artificial Technology Developments That Are Quietly Changing Everyday Life