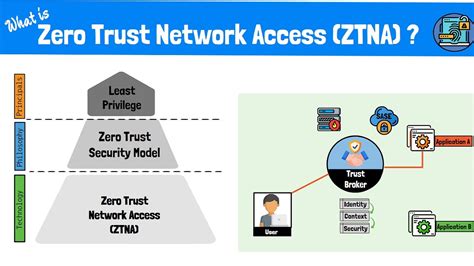
Mastering ZTNA: A Step-by-Step Implementation Strategy Guide
In today’s complex digital landscape, traditional perimeter-based security models are no longer sufficient to protect valuable assets from sophisticated cyber threats. The rise of remote work, cloud adoption, and mobile devices has dissolved the clear boundaries that once defined corporate networks. This evolution necessitates a fundamental shift in how organizations approach security, leading to the…