Mastering Enterprise CSPM: Essential Cloud Security Solutions
In today’s fast-paced digital landscape, enterprises are increasingly leveraging the scalability and flexibility offered by cloud computing. However, this shift introduces significant security challenges, making robust Enterprise Cloud Security Posture Management (CSPM) solutions not just beneficial, but absolutely essential for maintaining a secure and compliant environment.
These specialized solutions are designed to address the unique complexities of cloud security, providing continuous visibility and control over an organization’s cloud infrastructure. By doing so, they help prevent misconfigurations and enforce security policies across various cloud service providers.
The Evolving Landscape of Cloud Security Challenges
Enterprises migrating to the cloud often face a dynamic and complex security environment. The shared responsibility model, while clear in theory, can lead to ambiguity regarding who is responsible for specific security controls, especially at scale.
Furthermore, the rapid deployment of cloud resources and the inherent elasticity of cloud environments often outpace traditional security tools and manual processes. This creates a fertile ground for misconfigurations, which remain a leading cause of data breaches in the cloud.
What is Enterprise Cloud Security Posture Management (CSPM)?
Enterprise Cloud Security Posture Management (CSPM) refers to a class of security tools and services specifically designed to identify and remediate risks in cloud environments. It provides continuous monitoring of an organization’s cloud infrastructure for compliance violations and security misconfigurations.
CSPM solutions offer a comprehensive view of the security posture across multi-cloud and hybrid cloud setups, ensuring that security policies are consistently applied and maintained. They act as an automated guardian, constantly checking for deviations from established security baselines.
Key Capabilities of Advanced CSPM Solutions
Modern CSPM solutions offer a powerful suite of features to enhance cloud security. Understanding these capabilities is crucial for selecting and implementing an effective solution within an enterprise.
Continuous Misconfiguration Detection
One of CSPM’s primary functions is to continuously scan cloud resources for misconfigurations that could expose sensitive data or create vulnerabilities. This includes improperly configured storage buckets, overly permissive access policies, and unpatched virtual machines.
By automating this detection, CSPM tools drastically reduce the manual effort required and provide real-time alerts on potential security gaps. This proactive approach helps organizations address issues before they can be exploited by malicious actors.
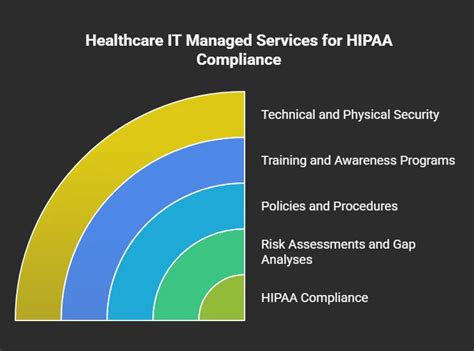
Compliance and Governance Automation
Enterprises operate under strict regulatory frameworks such as GDPR, HIPAA, PCI DSS, and various industry-specific standards. CSPM solutions automate the assessment of cloud environments against these compliance benchmarks, identifying non-compliant resources.
They provide detailed reports and evidence of compliance, simplifying audits and reducing the burden on security teams. This ensures that an organization’s cloud footprint adheres to all necessary legal and industry mandates.
Risk Prioritization and Remediation
Not all security findings are equally critical; some pose a higher risk than others. Advanced CSPM platforms use contextual intelligence to prioritize risks based on factors like potential impact, asset criticality, and exploitability.
Many solutions also offer automated or guided remediation steps, allowing security teams to quickly fix identified issues. This prioritization helps organizations focus their efforts on the most impactful vulnerabilities first, optimizing security resource allocation.
Threat Detection and Vulnerability Management
Beyond misconfigurations, some CSPM solutions integrate capabilities for detecting active threats and managing vulnerabilities within cloud workloads. They can identify suspicious activities, anomalous behaviors, and known software vulnerabilities.
This broader scope helps in creating a more unified security strategy, moving beyond just posture management to incorporate elements of threat intelligence. Integrating these aspects provides a more holistic view of the cloud security landscape.
Multi-Cloud and Hybrid Cloud Support
Most large enterprises operate across multiple public cloud providers (AWS, Azure, Google Cloud) and often maintain hybrid environments. An effective CSPM solution must provide unified visibility and consistent policy enforcement across all these diverse platforms.
This capability eliminates siloed security efforts and ensures that a single pane of glass can be used to manage the security posture of the entire cloud estate. It simplifies management and reduces the potential for inconsistencies.
The Tangible Benefits of Adopting CSPM
Implementing Enterprise Cloud Security Posture Management solutions brings a multitude of benefits that extend beyond just preventing breaches. These advantages contribute to overall business resilience and operational efficiency.
Organizations experience improved security posture, reduced operational costs due to automation, and a significant boost in compliance adherence. This allows security teams to be more strategic and less reactive.
How CSPM Integrates with Your Existing Security Stack
CSPM is a critical component of a comprehensive cloud security strategy, but it’s not a standalone solution. It often works in tandem with other cloud security tools like Cloud Workload Protection Platforms (CWPP), Cloud Infrastructure Entitlement Management (CIEM), and Cloud-Native Application Protection Platforms (CNAPP).
While CSPM focuses on the configuration of the cloud control plane, CWPP secures workloads (VMs, containers), CIEM manages identities and permissions, and CNAPP offers an end-to-end security framework. Together, these tools provide layered defense for the entire cloud environment.
Selecting the Right CSPM Solution for Your Enterprise
Choosing the appropriate CSPM solution requires careful consideration of an enterprise’s specific needs and existing cloud footprint. Key factors include scalability, multi-cloud compatibility, depth of policy enforcement, and integration capabilities with other security tools.
It is also important to evaluate the solution’s reporting features, automation capabilities for remediation, and the vendor’s support and roadmap. A thorough assessment ensures the selected CSPM can grow and adapt with the enterprise’s evolving cloud strategy.
Conclusion
Enterprise Cloud Security Posture Management (CSPM) solutions are indispensable for any organization serious about securing its cloud assets. They provide the necessary visibility, automation, and control to navigate the complexities of modern cloud environments.
By preventing misconfigurations, ensuring compliance, and providing continuous monitoring, CSPM empowers enterprises to harness the full potential of the cloud securely and confidently. Investing in a robust CSPM solution is an investment in the future resilience and integrity of your digital infrastructure.
Frequently Asked Questions (FAQ)
What is the primary goal of Enterprise CSPM solutions?
The primary goal of Enterprise Cloud Security Posture Management (CSPM) solutions is to continuously monitor, identify, and remediate security risks and misconfigurations across an organization’s entire cloud infrastructure. This ensures a strong and compliant security posture.
How does CSPM differ from traditional on-premise security tools?
CSPM is specifically designed for the dynamic, API-driven nature of cloud environments, focusing on configurations and policies within IaaS, PaaS, and SaaS layers. Traditional tools are often designed for static, perimeter-based on-premise networks and lack the visibility and automation needed for cloud’s ephemeral resources and shared responsibility model.
Can CSPM solutions help with regulatory compliance?
Yes, a core feature of CSPM solutions is their ability to automate compliance checks against various regulatory standards like GDPR, HIPAA, PCI DSS, and SOC 2. They identify non-compliant resources and provide reports that simplify auditing processes.
Is CSPM effective for multi-cloud environments?
Absolutely. Modern CSPM solutions are built to provide unified visibility and consistent policy enforcement across multiple public cloud providers (e.g., AWS, Azure, Google Cloud) and often hybrid cloud setups. This is a critical capability for most enterprises today.
What are common misconfigurations detected by CSPM?
Common misconfigurations detected include publicly exposed storage buckets, overly permissive Identity and Access Management (IAM) policies, unencrypted data stores, security groups with open ports, and instances lacking security updates or proper logging configurations.