Mastering ZTNA: A Step-by-Step Implementation Strategy Guide
In today’s complex digital landscape, traditional perimeter-based security models are no longer sufficient to protect valuable assets from sophisticated cyber threats. The rise of remote work, cloud adoption, and mobile devices has dissolved the clear boundaries that once defined corporate networks. This evolution necessitates a fundamental shift in how organizations approach security, leading to the prominence of Zero Trust Network Access (ZTNA).
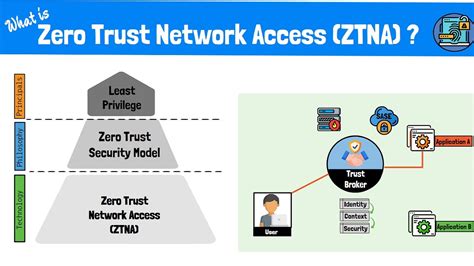
Zero Trust Network Access, often simply referred to as ZTNA, is a security model based on the principle of “never trust, always verify.” This means no user or device, whether inside or outside the network perimeter, is inherently trusted. Every access attempt, to any resource, must be authenticated and authorized based on strict policies.
Understanding Zero Trust Network Access (ZTNA)
ZTNA fundamentally redefines network security by moving away from the implicit trust granted to users and devices once they are inside the traditional network boundary. Instead, it enforces a granular, identity-centric approach to resource access. This security paradigm ensures that all access requests are explicitly validated before granting entry to specific applications or data.
Unlike conventional virtual private networks (VPNs) that grant broad network access, ZTNA provides secure, least-privilege access to individual applications. It creates a secure, encrypted tunnel directly to the requested application, rather than the entire network. This method significantly reduces the attack surface and prevents unauthorized lateral movement within the network, even if an endpoint is compromised.
Why Implement ZTNA? The Compelling Benefits
Adopting a Zero Trust Network Access strategy offers a multitude of benefits, addressing many of the challenges posed by modern IT environments. It significantly enhances an organization’s security posture against evolving threats. By eliminating implicit trust, ZTNA reduces the risk of data breaches and unauthorized access, even from within the network.
Furthermore, ZTNA improves the user experience by providing seamless and secure access to applications from any location, on any device. It supports a flexible work environment without compromising security, making it ideal for remote and hybrid workforces. The architecture also simplifies compliance efforts by enforcing strict access controls and providing detailed audit trails of all access attempts, aligning with various regulatory requirements.
Core Principles Driving ZTNA Deployment
The success of any ZTNA implementation hinges on adherence to its foundational principles. These tenets guide the design and operation of a truly secure network. The first principle is to verify explicitly, meaning all users and devices must be authenticated and authorized before gaining access to any resource, regardless of their location.
The second core principle is to use least privileged access, ensuring users are only granted the minimum level of access required to perform their specific tasks. This minimizes the potential impact if an account is compromised. Lastly, ZTNA operates on the assumption of a breach; it continuously monitors and validates every connection, treating all traffic as untrusted until proven otherwise.
A Step-by-Step ZTNA Implementation Strategy
Implementing ZTNA is a transformational journey that requires careful planning and execution. Following a structured approach can ensure a smooth transition and maximize the security benefits. This phased strategy begins with a thorough understanding of an organization’s current IT landscape and security needs.
Phase 1: Assessment and Planning
Begin by conducting a comprehensive assessment of your current network infrastructure, applications, and user base. Identify critical assets, define access requirements for different user roles, and map out existing data flows. This initial phase also involves setting clear objectives for your ZTNA rollout, establishing measurable success metrics, and gaining buy-in from key stakeholders across the organization.
Develop a phased rollout plan that prioritizes high-value assets and applications, allowing for incremental adoption and minimizing disruption. It is crucial to identify potential integration points with existing security tools and identity providers. A detailed inventory of all users, devices, applications, and their interdependencies will form the bedrock of your ZTNA strategy.
Phase 2: Identity and Access Management (IAM) Integration
Central to ZTNA is robust identity verification; therefore, strong integration with your existing Identity and Access Management (IAM) system is paramount. Ensure all user identities are accurately managed and that multi-factor authentication (MFA) is universally enforced for all access requests. This significantly strengthens the security posture against compromised credentials.
Leverage your IAM solution to establish user roles, attributes, and group policies that will inform your ZTNA access decisions. The identity of the user and their associated attributes will be a primary factor in determining access privileges. Strong authentication mechanisms, such as biometrics or hardware tokens, should be prioritized to enhance identity assurance.
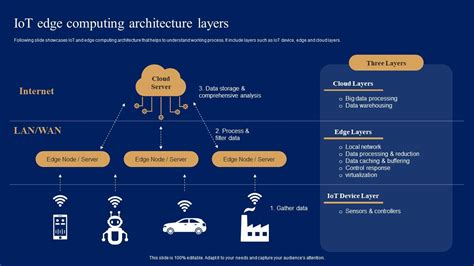
Phase 3: Microsegmentation and Resource Protection
Implement microsegmentation to logically divide your network into smaller, isolated segments, limiting lateral movement for potential attackers. This involves defining granular access policies for specific applications and resources, rather than broad network segments. Each segment can then have its own distinct security controls, making it much harder for threats to spread.
Identify all applications and data that require protection and configure ZTNA policies to grant access only to these specific resources. Prioritize critical applications and sensitive data, ensuring they are shielded behind the ZTNA framework. This targeted approach prevents unauthorized access to resources not explicitly needed by the user or device.
Phase 4: Policy Definition and Enforcement
Develop precise, context-aware access policies that consider user identity, device posture, location, time of day, and the sensitivity of the requested application. These policies are the brain of your ZTNA system, determining who can access what, under what conditions. Continuously monitor and enforce these policies in real-time to adapt to changing threat landscapes and user behaviors.
Ensure that policies follow the principle of least privilege, granting only the necessary access for users to perform their duties. Regular reviews of these policies are essential to ensure they remain relevant and effective. Automated policy enforcement tools can greatly simplify the management of complex access rules across dynamic environments.
Phase 5: Monitoring, Analytics, and Threat Detection
Establish comprehensive monitoring and logging capabilities to track all access attempts, user behavior, and network traffic. Utilize advanced analytics to detect anomalies, identify potential threats, and respond proactively to security incidents. This continuous vigilance is vital for maintaining a strong security posture.
Integrate ZTNA logs with your Security Information and Event Management (SIEM) system for centralized visibility and automated threat correlation. The insights gained from monitoring will help refine policies and improve overall security effectiveness. Real-time alerts are crucial for promptly addressing any suspicious activities or policy violations.
Phase 6: Continuous Improvement and Adaptation
ZTNA implementation is not a one-time project but an ongoing process of refinement and adaptation. Regularly review your ZTNA architecture, policies, and security controls to align with evolving business needs and emerging threat vectors. Update policies as new applications are introduced or user roles change.
Regularly conduct security audits and penetration testing to identify weaknesses and validate the effectiveness of your ZTNA deployment. Foster a culture of security awareness among employees, ensuring they understand their role in maintaining a secure environment. The security landscape is dynamic, and your ZTNA strategy must be equally agile to remain effective.
Overcoming Common ZTNA Implementation Challenges
While the benefits are clear, organizations often face challenges during ZTNA adoption. Legacy systems and complex existing network architectures can complicate the integration of new ZTNA solutions. Phased implementation and careful planning can mitigate these issues, prioritizing critical systems first.
Another common hurdle is organizational resistance to change, particularly from users accustomed to less restrictive access. Effective communication and user education are essential to explain the benefits and ease the transition. Additionally, selecting the right ZTNA vendor and solution that integrates well with your existing ecosystem is paramount for a successful deployment.
The Future of Network Security is Zero Trust
Zero Trust Network Access represents the future of secure connectivity, moving beyond outdated perimeter defenses to embrace an adaptive, identity-centric approach. By implementing a robust ZTNA strategy, organizations can significantly strengthen their security posture, protect critical assets, and empower their workforce with flexible, secure access. The journey to Zero Trust is an investment in resilient, future-proof cybersecurity.
Frequently Asked Questions (FAQ)
What is Zero Trust Network Access (ZTNA)?
ZTNA is a security model that operates on the principle of “never trust, always verify.” It means no user or device, whether inside or outside the network, is implicitly trusted. Every attempt to access a resource must be authenticated and authorized based on strict, granular policies, ensuring least-privilege access.
How is ZTNA different from a traditional VPN?
Traditional VPNs grant broad network access once a user authenticates, effectively extending the corporate perimeter to the remote user. ZTNA, however, provides granular, least-privilege access directly to specific applications or services, not the entire network. This significantly reduces the attack surface and prevents lateral movement, offering superior security compared to VPNs.
What are the core principles of Zero Trust?
The core principles of Zero Trust are: 1) Verify explicitly (authenticate and authorize all users and devices); 2) Use least privileged access (grant only the minimum access needed); and 3) Assume breach (continuously monitor and validate every connection, preparing for potential compromises).
What are the main benefits of implementing ZTNA?
Implementing ZTNA offers several key benefits, including enhanced security through reduced attack surface and prevention of lateral movement, improved user experience with seamless and secure access from anywhere, better compliance with strict access controls and audit trails, and increased agility for hybrid and remote work models.
What are some common challenges in ZTNA deployment?
Common challenges include integrating ZTNA with complex legacy systems, overcoming organizational resistance and user discomfort with new access controls, and the critical process of selecting the right ZTNA vendor and solution that aligns with existing infrastructure and security needs.
Can ZTNA integrate with existing security infrastructure?
Yes, ZTNA is designed to integrate with existing security tools, particularly Identity and Access Management (IAM) systems for user authentication and authorization, and Security Information and Event Management (SIEM) systems for comprehensive logging and threat detection. This integration allows for a cohesive and stronger security posture.